The recipient can decrypt the digital signature and perform the same perform to verify the hash value using the sender’s public key. Actually speaking, it’s an concept that’s removed from actuality at the moment. Nonetheless, the potential of quantum computing to break asymmetric encryption algorithms is a growing concern that your organization wants to concentrate on. While quantum computer systems capable of breaking present cryptographic techniques do not exist but, their development might have important implications on your long-term safety technique. Analysis into post-quantum cryptography is critical for long-term enterprise resilience. It remains critical to examination prep and real-world governance selections.
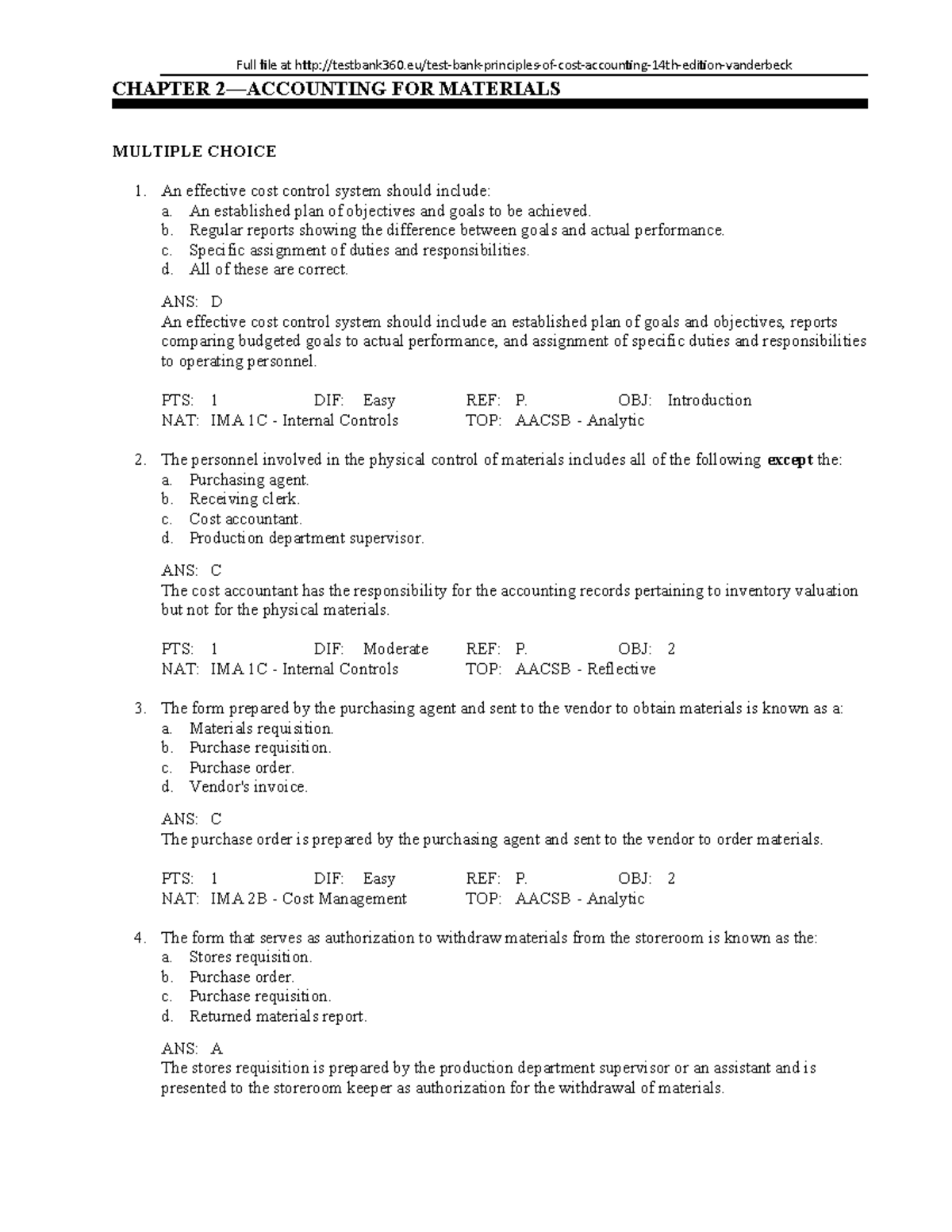
Cloud Hsms And Compliance
When you implement and manage them accurately, you give your customers, partners, and shoppers the arrogance that every digital interplay with your organization is secure, authentic, and verifiable. Let’s make one of many keys public, meaning literally anybody can see it, and keep the opposite a secret. This is done in a number of ways, depending on how you plan to use the keys. For instance there are public key servers for sure encryption tools that you just might upload your own public key to. For web sites there are the so-called “root certificates” current in the operating system that are a half of the mechanism that make website public keys public. You’re most likely used to traditional encryption, where you encrypt one thing using a password and you utilize that same password to decrypt it.
Certificate Revocation Lists (crls)
- It is the main ingredient of digital signatures and way more safe than symmetric encryption.
- In theory, figuring out the public key permits the calculation of the non-public key’s value, but due to the complexity of the algorithms concerned, it usually takes a substantial amount of time.
- Personal keys usually are not shared and could be saved within the software program or working system that is used, or on hardware similar to a hardware safety module (HSM) that provides greater ranges of knowledge security and trust.
- It is a symmetric cipher, meaning both events use the same code to send and receive messages that either can learn.
- Only my secret key can be utilized to decrypt one thing encrypted utilizing my public key.
Ciphers are extra complicated and use a mathematical algorithm to both substitute for the original information and multiply that end result by another quantity that is the key to the algorithm. They can’t even decrypt knowledge they themselves encrypted, that means key A cannot be used to decrypt knowledge encrypted utilizing key A. Let’s dive into what public key cryptography is, why it’s helpful, and the way it’s being used. The “How” is already defined well by others, but as far I can see, nobody wrote about “What does uneven encryption do?”. To break ECC, an attacker must compute an elliptic curve discrete logarithm, which is considerably tougher than factoring.
Ssl/tls Certificates Secure Your Website

The recipient of the message can decrypt the message using their associated non-public key. The session keys are symmetric and are what the consumer and server use for all information exchanges for that specific session. No intruder can decrypt or guess the session key while it is in transit between the browser and the server. This helps to guard your data from being intercepted and browse in man-in-the-middle attacks (also often recognized as MitM attacks). So, the method starts out with uneven encryption and modifications to symmetric encryption for the majority of the data exchange. Let’s take an example of how asymmetric key encryption works in actual life.
Symmetric cryptography is quicker to run (in terms of each encryption and decryption) because the keys used are much shorter than they are in uneven cryptography. Moreover, the fact that just one key gets used (versus two for asymmetric cryptography) additionally makes the whole process quicker. Elliptic curve cryptography (ECC) is gaining favor with many safety consultants as a substitute for RSA. ECC is a public key encryption technique primarily based on elliptic curve theory. It can create quicker, smaller and more efficient cryptographic keys by way of the properties of the elliptic curve equation.
It’s how world organizations scale safe communication throughout hundreds of users with out ballooning operational costs or compliance gaps. Public-key cryptography is a type of https://indianhelpline.in/business-contact/25475-data-patterns-india-limited/ information encryption know-how used to guard confidential information. Information encryption refers to utilizing a code as a key to guard necessary information and restrict access to a certain person or group of customers.
Knowledge Protection andamp; Security Laws
This interdependence supplies quite lots of benefits, an important of that are most likely digital signatures. Digital signatures are used to make certain that a message was created by a particular entity and to authenticate remote systems or users, amongst different issues. What makes public-key encryption safe, is that there is primarily an infinite number of prime numbers available… which theoretically means that there are nearly infinite potentialities for keys. At a fundamental degree, the consumer (i.e. your browser) and the server negotiate a key trade algorithm to derive a random session key and then they use that private key to encrypt traffic with a symmetric algorithm. The idea was independently and covertly proposed by James Ellis a quantity of years earlier, whereas he was working for the Government Communications Headquarters, the British intelligence and security organization.
Collectively, the two events then generate the master secret (a shared secret) and similar session keys. You may feel confident today knowing your encryption keys are strong sufficient to face up to any attack. When quantum machines mature, algorithms like Shor’s will make breaking RSA and ECC keys potential in hours as an alternative of millennia. Every encrypted backup, certificate, and signed transaction your organization depends on might all of a sudden turn into readable.This isn’t a far-off principle anymore. Governments, protection contractors, and monetary institutions are already making ready for what’s referred to as the “Q-Day” — the second when quantum capabilities can break classical encryption.
Truthfully, you don’t need to know public key cryptography apart from to realize it’s a key part of keeping you secure online. Different operations are possible (such as encryption) with the same key datarequired for verification, however not presently supported, and others(eg. decryption and signature generation) require extra key data. In such a case, the uneven key would thenmerely be an interface to the TPM driver.
The algorithm will encode the message, which might now be sent to Company A. The key to unlocking it is x and y, which only Firm A is conscious of, so the company can decipher the message. The message stays secure as a result of factoring z to x and y is tough and time consuming. Only I can decrypt it as a result of solely I truly have the key key that goes along with the public key I made obtainable for anybody to use. Only my secret key can be utilized to decrypt one thing encrypted using my public key. Asymmetric means you use a unique encryption key to encrypt than you to do decrypt. Symmetric encryption, on the opposite hand, uses the same password to encrypt and to decrypt — similar to a password-protected document or zip file.